- Cryptanalysis of the Lorenz cipher
-
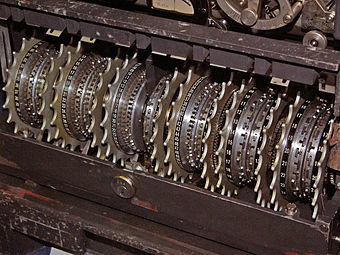 The Lorenz SZ machines had 12 wheels each with a different number of cams (or pins).
The Lorenz SZ machines had 12 wheels each with a different number of cams (or pins).
Wheel number 1 2 3 4 5 6 7 8 9 10 11 12 BP wheel name[1] ψ1 ψ2 ψ3 ψ4 ψ5 μ37 μ61 χ1 χ2 χ3 χ4 χ5 Number of cams (pins) 43 47 51 53 59 37 61 41 31 29 26 23 Cryptanalysis of the Lorenz cipher was the process that enabled the British to read secret German military messages during World War II. The British Government Code and Cypher School at Bletchley Park decrypted many communications between the German High Command in Berlin and their army commands throughout occupied Europe. These were intercepted non-Morse radio messages that had been enciphered by the Lorenz SZ teletypewriter rotor cipher attachments. British cryptographers referred to encrypted German teleprinter traffic as "Fish". They dubbed this machine and its traffic "Tunny", and the intelligence it yielded as "Ultra".[2]
As with the entirely separate Cryptanalysis of the Enigma, it was German operational shortcomings that allowed the initial diagnosis of the system, and a way into decryption.[3] Unlike Enigma, however, no physical machine reached allied hands until the very end of the war in Europe, long after wholesale decryption had been established.
The message characters were encoded in the 5-bit International Telegraphy Alphabet No. 2 (ITA2). The cipher attachments implemented a type of Vernam stream cipher using a complex array of twelve wheels. The right hand five of these, the chi (χ) wheels, changed the five bits of the incoming character, advancing one position with each one. The left hand five, the psi (ψ) wheels, changed the result of the chi transform further. The central two mu (μ) or "motor" wheels determined whether the psi wheels rotated with a new character.[4]
Initially, operator errors produced a number of pairs of messages sent with the same keys, giving a so-called "depth", which often allowed manual decryption to be achieved. Such depths also allowed the complete logical structure of the machine to be worked out, a quite remarkable cryptanalytical feat on which the subsequent bulk decryption of Tunny messages relied.[5]
Subsequently, decryption was achieved by a combination of manual and automated methods. The effect of the chi component of the key was removed with the use of machines that implemented a statistical technique. The first machine was called "Heath Robinson" and it was followed by several other "Robinsons". These were, however, slow and unreliable, and were superseded by "Colossus" the world's first electronic, (semi-)programmable computer, ten of which were in use by the end of the war.[6] The psi component was then removed using manual methods and machines that imitated the Tunny machine - the so-called "British Tunny" machines.[7]
Secure Telegraphy
See also: Electrical telegraphElectro-mechanical telegraphy was developed in the 1830s and 1840s, well before telephony, and was in widespread use all over the world by the time of the Second World War. An extensive system of cables were used within and between countries, but for mobile German Army Units, radio transmission was often used.
Teleprinters at each end of the circuit consisted of a keyboard and printing mechanism, and very often a five-hole paper tape reading and punching mechanism. When used online, pressing an alphabet key at the transmitting end caused the relevant character to be printed at the receiving end. Commonly, however, the transmitting operator would prepare a message offline by punching it onto paper tape, and then going online only for the transmission of the message recorded on the tape. Typically this would be at some ten characters per second, and so occupy the line or radio channel for a shorter time than for online typing.
The characters of the message were represented by the codes of the International Telegraphy Alphabet No. 2 (ITA2). The transmission medium, either wire or radio, used asynchronous serial communication with each character signaled by a start bit, 5 data bits and 1½ stop bits. Each bit was either a "mark" (hole in paper tape, 1 in binary or x at Bletchley Park) or a "space" (no hole in tape, binary 0 or • at Bletchley Park). For example the letter "H" would be coded as ••x•x.[8]
International telegraphy alphabet No. 2 with terminology and conventions used at Bletchley Park (BP) Pattern of impulses Mark = x, Space = • Binary Letter shift Figure shift BP 'shiftless' interpretation ••••• 00000 null null / ••x•• 00100 space space 9 ••x•x 00101 H # H ••••x 00001 T 5 T •••xx 00011 O 9 O ••xxx 00111 M M ••xx• 00110 N , N •••x• 00010 CR CR 3 •x•x• 01010 R 4 R •xxx• 01110 C : C •xxxx 01111 V ; V •x•xx 01011 G & G •x••x 01001 L ) L •xx•x 01101 P 0 P •xx•• 01100 I 8 I •x••• 01000 LF LF 4 xx••• 11000 A - A xxx•• 11100 U 7 U xxx•x 11101 Q 1 Q xx••x 11001 W 2 W xx•xx 11011 FIGS + or 5 xxxxx 11111 LTRS - or 8 xxxx• 11110 K ( K xx•x• 11010 J ' J x••x• 10010 D $ D x•xx• 10110 F ! F x•xxx 10111 X / X x••xx 10011 B ? B x•••x 10001 Z " Z x•x•x 10101 Y 6 Y x•x•• 10100 S ' S x•••• 10000 E 3 E The figure shift (FIGS) and letter shift (LETRS) characters determined how the receiving end should interpret the string of characters up to the next shift character. Because of the danger of a shift character being corrupted, some operators would send a pair of shift characters when changing from letters to numbers or vice versa. Such doubling of characters was helpful to the cryptanalysts at Bletchley Park's statistical analysis. After encipherment, shift characters had no special meaning.
For its secret transmissions, the German armed services enciphered each character using various online Geheimschreiber (secret writer) machines at both the transmitting and receiving ends. These were the Lorenz SZ (SZ for Schlüsselzusatz, meaning "cipher attachment") machine for the army, the Siemens and Halske T52 for the air force and the Siemens T43 which was little used and never broken by the Allies.[9] Enigma decrypts had revealed that the Germans called the wireless teleprinter transmission systems "Sägefisch" (sawfish), so the name "Fish" was adopted for this traffic.[10] "Tunny" was the name given at Bletchley Park to the first non-Morse link, and it was subsequently used for all traffic enciphered with the Lorenz SZ machines.
References and Notes
- ^ Good, Michie & Timms 1945, p. 6 of German Tunny
- ^ Hinsley 1993, p. 141-142
- ^ Copeland 2006, p. 45
- ^ Good 1993, p. 153
- ^ Tutte 1998, pp. 5, 6
- ^ All but two of the Colossus computers, which were taken to GCHQ, were destroyed in 1945, and the whole project was kept strictly secret until the 1970s, and so Colossus did not feature in many early descriptions of the development of electronic computers.
- ^ Wylie 2001, pp. 289–304
- ^ Copeland 2006, pp. 348, 349
- ^ Weierud 2006, p. 307 in Copeland 2006, pp. 307–327
- ^ Gannon 2006, p. 102
Bibliography
- Carter, Frank, Bletchley Park Technical Papers: Colossus and the Breaking of the Lorenz Cipher, http://www.bletchleypark.org.uk/content/lorenzcipher.pdf, retrieved 28 January 2011
- Churchhouse, Robert (2002), Codes and Ciphers: Julius Caesar, the Enigma and the Internet, Cambridge: Cambridge University Press, ISBN 978-0-521-00890-7
- Copeland, B. Jack, ed. (2006), Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4
- Erskine, Ralph; Smith, Michael, eds. (2011) [2001], The Bletchley Park Codebreakers, Biteback Publishing Ltd, ISBN 978 184954078 0 Updated and extended version of Action This Day: From Breaking of the Enigma Code to the Birth of the Modern Computer Bantam Press 2001
- Gannon, Paul (2007), Colossus: Bletchley Park's Greatest Secret, Atlantic Books, ISBN 978 1843543312
- Good, Jack; Michie, Donald; Timms, Geoffrey (1945), General Report on Tunny: With Emphasis on Statistical Methods, UK Public Record Office HW 25/4 and HW 25/5, http://www.alanturing.net/turing_archive/archive/index/tunnyreportindex.html, retrieved 15 September 2010 That version is a facsimile copy, but there is a transcript of much of this document in '.pdf' format at: Sale, Tony (2001), Part of the "General Report on Tunny", the Newmanry History, formatted by Tony Sale, http://www.codesandciphers.org.uk/documents/newman/newman.pdf, retrieved 20 September 2010, and a web transcript of Part 1 at: Ellsbury, Graham, General Report on Tunny With Emphasis on Statistical Methods, http://www.ellsbury.com/tunny/tunny-001.htm, retrieved 3 November 2010
- Good, Jack (1993), Enigma and Fish in Hinsley & Stripp 1993, pp. 149–166
- Government Code and Cypher School (1944), The Bletchley Park 1944 Cryptographic Dictionary formatted by Tony Sale, http://www.codesandciphers.org.uk/documents/cryptdict/cryptxp3.pdf, retrieved 7 October 2010
- Hinsley, F.H.; Stripp, Alan, eds. (1993) [1992], Codebreakers: The inside story of Bletchley Park, Oxford: Oxford University Press, ISBN 978-0-19-280132-6
- Hinsley, F.H. (1993), "Introduction: The influence of Ultra in the Second World War" in Hinsley & Stripp 1993, pp. 1–13
- Newman, Max (c. 1944), Appendix 7: Δχ-Method in Copeland 2006, pp. 386–390
- Tutte, William T. (2006), Appendix 4: My Work at Bletchley Park in Copeland 2006, pp. 352–369
- Tutte, W. T. (19 June 1998), Fish and I, http://frode.home.cern.ch/frode/crypto/tutte.pdf, retrieved 7 October 2010 Transcript of a lecture given by Prof. Tutte at the University of Waterloo
- Weierud, Frode (2006), Bletchley Park's Sturgeon—The Fish That Laid No Eggs in Copeland 2006, pp. 307–327
- Wylie, Shaun (2001), Breaking Tunny and the birth of Colossus in Erskine & Smith 2011, pp. 283–304
Categories:- History of cryptography
- Signals intelligence of World War II
- Bletchley Park
Wikimedia Foundation. 2010.
