- Pigpen cipher
-
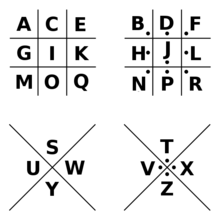
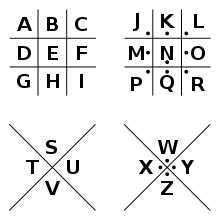 The pigpen cipher uses graphical symbols assigned according to a key similar to the above diagram.[1]
The pigpen cipher uses graphical symbols assigned according to a key similar to the above diagram.[1]
The pigpen cipher (sometimes referred to as the masonic cipher, Freemason's cipher, Rosicrucian cipher, or Tic-tac-toe cipher)[2][3] is a geometric simple substitution cipher which exchanges letters for symbols which are fragments of a grid. The example key shows one way the letters can be assigned to the grid.
Contents
Security
The use of symbols is no impediment to cryptanalysis, and this system is identical to that of other simple monoalphabetic substitution schemes. Due to the simplicity of the cipher, it is often included in children's books on ciphers and secret writing.[4]
History
The exact origin of the cipher is uncertain,[5] but records of this system have been found which go back to at least the 18th century. Variations of this cipher were used by both the Rosicrucian brotherhood[5] and the Freemasons, though the latter used it so often that the system is frequently called the Freemason's cipher. They began using it in the early 18th century to keep their records of history and rites private, and for correspondence between lodge leaders.[3][6][7] Tombstones of Freemasons can also be found, which use the system as part of the engravings. One of the earliest stones in Trinity Church Cemetery in New York City, which opened in 1697, contains a cipher of this type which deciphers to "Remember death". George Washington's army had documentation about the system, with a much more randomized form of the alphabet. And during the American Civil War, the system was used by Union prisoners in Confederate prisons.[5]
Variants
The core elements of this system are the grid and dots. Some systems use the X's, but even these can be rearranged. One commonly used method orders the symbols as shown in the above image: grid, grid, X, X. Another commonly used system orders the symbols as grid, X, grid, X. Another is grid, grid, grid, with each cell having a letter of the alphabet, and the last one having an "&" character. Letters from the first grid have no dot, letters from the second each have one dot, and letters from the third each have two dots. Another variation of this last one is called the Newark Cipher, which instead of dots uses one to three short lines which may be projecting in any length or orientation. This gives the illusion of a larger number of different characters than actually exist.[8]
Another system, used by the Rosicrucians, used a single grid of nine cells, and 1 to 3 dots in each cell or "pen". So ABC would be in the top left pen, followed by DEF and GHI on the first line, then groups of JKL MNO PQR on the second, and STU VWX YZ on the third.[2][5] When enciphered, the location of the dot in each symbol (left, center, or right), would indicate which letter in that pen was represented.[1][5] More difficult systems use a non-standard form of the alphabet, such as writing it backwards in the grid, up and down in the columns,[4] or a completely randomized set of letters.
Example
Using the example key in the above image, the message "X marks the spot" is rendered in ciphertext as:
In popular culture
The Pigpen cipher has been used in several works of popular culture including Dan Brown's 2009 novel The Lost Symbol, both in the book itself, and also to provide a puzzle in the artwork of the U.S. version of the bookjacket. The Trap, a 2009 nominee for Lancashire Children's Book of the Year, uses a variation of the Pigpen cipher.[9]
In the game Assassin's Creed II, the cipher is used in the hidden glyph puzzle number 10, titled "Apollo". Here the cipher is one of many hidden messages tucked away in paintings and photos of historic events or people. Though not essential to the play of the game, the encrypted messages, some of which also use Morse Code and binary code, provide clues to the game's back-story.
The BBC series, Sherlock, has created a website to correlate with the events in the series - The Science of Deduction. Under the "Hidden Messages" tab, "Sherlock" lists three coded messages he received from a stalker, and the third is in pigeon cipher.
In Club Penguin, a modified pigpen cipher is used for "Secret Agents".
Notes
References
- Barker, Wayne G., ed (1978). The History of Codes and Ciphers in the United States Prior to World War I. Aegean Park Press. ISBN 0894120263.
- Gardner, Martin (1972). Codes, ciphers and secret writing. ISBN 0-486-24763-9.
- Kahn, David (1967). The Codebreakers. The Story of Secret Writing. Macmillan.
- Kahn, David (1996). The Codebreakers. The Story of Secret Writing. Scribner. ISBN 0684831309.
- Newton, David E. (1998). "Freemason's Cipher". Encyclopedia of Cryptology. ISBN 0-87436-772-7.
- Pratt, Fletcher (1939). Secret and Urgent: The story of codes and ciphers. Aegean Park Press. ISBN 0894122614.
- Shulman, David; Weintraub, Joseph (1961). A glossary of cryptography. Crypto Press. pp. 44.
- Wrixon, Fred B. (1998). Codes, Ciphers, and other Cryptic & Clandestine Communication. Black Dog & Leventhal Publishers, Inc.. ISBN 1579120407.
External links
- The Elian Script is a similar grid-based cipher, used as art.
- Online Pigpen cipher tool for enciphering small messages.
- Cipher Code True Type Font
- FF Text Converter converts text in pigpen cipher and more.
Classical cryptography Ciphers: ADFGVX · Affine · Alberti · Atbash · Autokey · Bifid · Book · Caesar · Dvorak · Four-square · Great · Hill · Keyword · Nihilist · One-time pad · Permutation · Pigpen · Playfair · Polyalphabetic · Polybius · Rail Fence · Reihenschieber · Reservehandverfahren · ROT13 · Running key · Scytale · Smithy code · Solitaire · Straddling checkerboard · Substitution · Tap code · Transposition · Trifid · Two-square · VIC cipher · Vigenère
Cryptanalysis: Frequency analysis · Index of coincidence · Kasiski examination
Misc: Cryptogram · Bacon · Scytale · Straddling checkerboard · Tabula recta
Cryptography Categories:- Classical ciphers
- Masonic symbolism
Wikimedia Foundation. 2010.